Secure Infrastructure
- Isolated VPCs and client data in the cloud, managed by a dedicated cloud engineering team.
- 256-bit encryption for data at rest and HTTPS with TLS 1.2 encryption for data in transit.
- Intrusion prevention/detection (IDS/IPS), anti-malware, and anti-virus monitored around the clock.
- Automated server patching.
- Modern OAuth protected API access.
Secure Product Development
- Product roadmap with product management team oversight of feature/fix priority.
- Secure software development lifecycle (SDLC).
- Secure coding practices and training for engineers.
- Dedicated quality assurance and user experience teams.
- Established change management policies and procedures with segregation of duties.
Resilient Architecture
- Cross-region, geographically isolated infrastructure redundancy
- Near real-time automated and geo-replicated data backups
- Firewall-protected modern load balancers
- Security operations center monitoring 24×7 with “eyes on glass”
- Dedicated cloud/DevOps team

Trust You Can Count On
Like many Software-as-a-Service providers, ensuring the security of our platform, supporting systems, and data is a shared responsibility among our team, our trusted cloud service provider, and our customers. With guidance from industry experts and adopting industry standard frameworks and best practices, SPARK has established a model that clearly articulates who is accountable for key security responsibilities across the environment.
Our Shared Responsibility Model Covers:
- Physical Infrastructure and Network Security and Resiliency;
- Application Security;
- User Accounts and Client Data Security;
- Governance, Compliance, and Data Privacy Protections.

SOC 2 & Due Diligence at SPARK
SPARK complies with SSAE 18 standards and maintains a SOC 2 Type 1 and Type 2 attestation of the SPARK platform. Visit the FAQ section to learn more.
To request a copy of our latest SOC 2 report or full standard due diligence package, email us at compliance@lendwithspark.com
Your Frequently Asked Questions
-
Answer: SOC 2® – SOC for Service Organizations: Trust Services Criteria SOC 2® reports are examination engagements performed by a service auditor in accordance with SSAE 18 and meet the needs of a broad range of users that need detailed information and assurance about the controls at a service organization relevant to security, availability, and processing integrity of the systems the service organization uses to process users’ data and the confidentiality and privacy of the information processed by these systems. These reports can play an important role in:
- Oversight of the organization
- Vendor management programs
- Internal corporate governance and risk management processes
- Regulatory oversight
-
Each user is given a unique username and password, which they alone control. Users can also enhance security using two-factor authentication.
-
No! You do not need to have a dedicated IT staff person to support the SPARK platform. SPARK has a dedicated support line that is staffed Monday – Friday from 8 AM – 5:30 PM CST. Additionally, each client has a dedicated customer success manager who is available to address any strategy questions associated with the SPARK platform.
-
We do not connect to a servicing system, but we can generate the information needed for servicing. Using our API, we can pull data out of SPARK, which can then be used for a servicing system.
-
Yes! SPARK has built-in integrations with DocuSign, FICO Liquid Credit, Laser Pro, TEA, and NLS. SPARK also supports API integrations that allow SPARK to communicate with third parties.
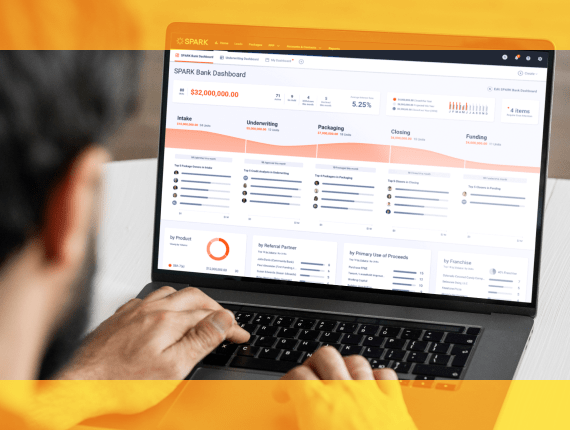
Experience the SPARK Difference
Want a secure, compliant, digital lending solution? SPARK delivers with the industry’s fastest, easiest platform. See for yourself.